In yet another incident in the growing ecosystem of decentralized finance (DeFi), TransitFinance has reportedly suffered a smart contract hack, which resulted in an estimated loss of around $1.88 million.
This incident, recently reported by blockchain security monitor PeckShield Alert, is a reminder that while current infrastructure may be robust, legacy code continues to proliferate in embedded form within blockchain networks.
#PeckShieldAlert @TransitFinance seems to have been hacked for ~$1.88M
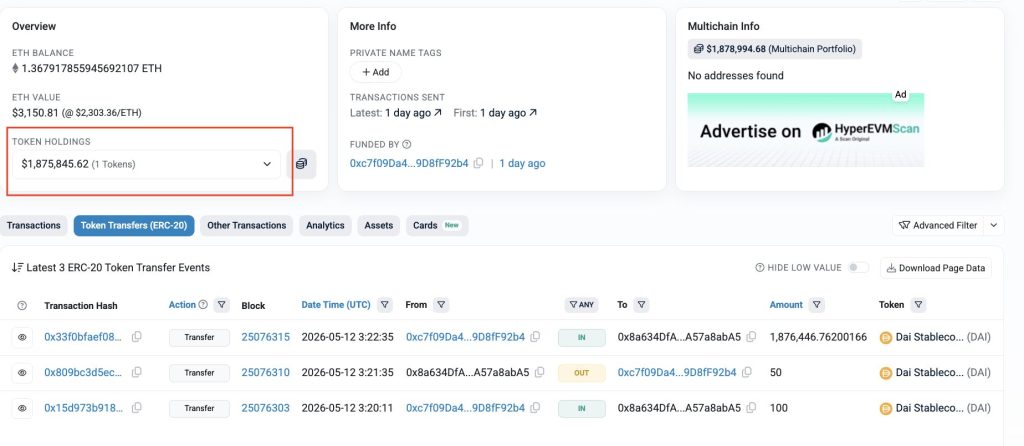
The stolen funds are currently sitting in the following address in $DAI: 0x8a634DfA2609358849D7D65FFA270C8A57a8abA5 pic.twitter.com/9RSQkgdfX6
— PeckShieldAlert (@PeckShieldAlert) May 13, 2026
TransitFinance says the hack came from an early smart contract deployed to the TRON network. This contract was officially deprecated in 2022 but still lingered on-chain and malicious actors were able to exploit the dormant vulnerability.This case study demonstrates an ongoing problem within DeFi: even when old contracts are not, and cannot, be used, they stay propagating because they can still get called upon unless made completely nonoperational or destroyed.
This attack takes advantage of the vulnerabilities built into a legacy contract, impacting only a subset of users.This case is an example of how “inactive” components can still provide a significant attack surface, unlike many exploits that affect live protocols. This way, the attacker has not hacked the current system but to hack an unprotected legacy contract remains open.
All Stolen Funds Have Been Merged Into A Single Address
The no reward analysis of the exploit considers consolidating original assets, which total follows $1.88 million, to a single wallet. Funds are deposited in DAI which is a popular, more stable and liquid stablecoin in DeFi.
This is a consolidation pattern showing us an orchestrated and systematic siphoning rather than a disordered, rapid, pointillistic theft across addresses. This also makes the trail of stolen money easier to follow, possibly allowing investigators to follow or even promptly intercept additional transfers.
But DAI could be used to launder via decentralized exchanges or cross-chain bridges, which would further complicate recovery and obscure the path of funds.
Immediate Response and Containment Measures ॑
TransitFinance reacted quickly when they detected the exploit. Following the incident, an official statement on TransitFinance Announcement indicates that the team had conducted extensive internal investigations, segregating compromised components. The protocol stressed that the contract in question is not a part of its current operating framework.
Your smart contract is still secure, backed by four plus years of uninterrupted audits, testing and monitoring with the latest version.The team conducted additional reviews and remediation, during which they reiterated that the platform’s active infrastructure was never compromised. That meant users were told that there was no urgent action required, signalling confidence in the containment process.
Transit Announcement Regarding a recent incident related to historical legacy risks, we would like to share the following update:
1⃣ Cause of the Incident
The issue was related to an early-version smart contract previously deployed on TRON. Although this legacy contract had…
— Transit (@TransitFinance) May 13, 2026
To regain the trust of their user base, TransitFinance promised to fully compensate all affected users. Exact timelines and processes have yet to be provided, but the team promised to update through official channels. Though compensation has emerged as a customary response to DeFi breaches, the manner in which it is executed will be critical for long-term community trust.
TransitFinance is presumably acting swiftly to protect its reputation and gain user confidence.Still, the cost of these reimbursements could add strain on to protocols struggling with balancing what they have in their treasuries against their ongoing operational needs.
Wider Impacts on DeFi Security
There is growing pressure on developers to keep a “clean” contract environment, meaning the old code can’t be used as a path for attack. This requires not just forward looking audits of active deployments but also retrospective scrutiny of all historical contracts.
The incident is a reminder to users that the risk in DeFi lives beyond visible interfaces. Vulnerabilities can remain dormant until used for an attack.
TransitFinance later even published a security alert warning users that they could face scams. This often leads to malicious actors taking advantage by posing as trusted news outlets, or sending fraudulent emails. NEVER share your keys or seed phrases with anyone, as this information gives access to your funds and cannot be recovered if lost.
The team recommends that officials only use verified messaging platforms to ensure they do not fall for further attacks since it is common for a secondary attack to happen after a high-profile breach.
Conclusion: Call to Protocol Hygiene
The exploit of TransitFinance may not be one of the biggest DeFi hacks, but its impact is heavy. This indicates that even well-maintained platforms can conceal risks if legacy systems are not being secured.
With the DeFi ecosystem expanding, it is time to transition focus away from pure innovation and growth into a protracted upkeep of existing infrastructure. Given that code is static and visible, your attack surface includes every contract deployed in a domain instead of just active contracts.
In the immediate crisis, it seems that TransitFinance has contained the damage. This is the message for the wider DeFi community: that security does not stop with upgrades but requires constant attention during the whole lifetime of a protocol.
Disclosure: This is not trading or investment advice. Always do your research before buying any cryptocurrency or investing in any services.
Follow us on Twitter @nulltxnews to stay updated with the latest Crypto, NFT, AI, Cybersecurity, Distributed Computing, and Metaverse news!