Cross-chain liquidity protocol THORChain has just faced a major exploit, with early reports suggesting over $10m in digital assets lost.
All incomes from the breach were withdrawn across blockchains-Bitcoin, Ethereum, BNB Chain, Base.
The exploit was first revealed to blockchain security analysts through a PeckShield alert and then confirmed by THORChain in its own subsequent protocol update.
#PeckShieldAlert @THORChain has been exploited for ~$10M worth of crypto, including 36.75 $BTC ($3M) and ~$7M worth of assets from #BNBChain, #Ethereum, and #Base.
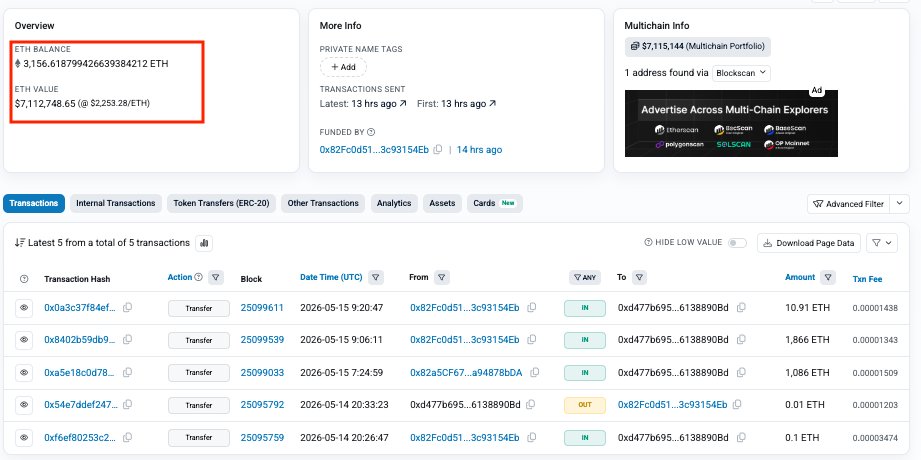
The stolen funds mainly sit in:
bc1ql4u94klk265lnfur2ujk9p6uh52f2a8jhf6f37… pic.twitter.com/mhWIWueVPK— PeckShieldAlert (@PeckShieldAlert) May 15, 2026
Independent investigator ZachXBT also issued a warning, via a ZachXBT alert, adding that total losses might exceed the original estimates. However, while this continues to be a fast-moving, fluid situation, early reports suggest users and funds were not directly at risk – which has been positive in terms of keeping community confidence from cratering straight after.
Can tell because they did not check the numbers themselves / chains listed.
I finished accounting again now and it looks to be $10M+ stolen at least.
— ZachXBT (@zachxbt) May 15, 2026
Exploit Targets Asgard Vault Infrastructure
Initial investigation suggests a compromise of one of the core infrastructure components within THORChain, specifically Asgard vault. Together, these vaults are managed by node operators to store and provide cross-chain liquidity across the network.
Which points to one of their six Asgard vaults being breached allowing outbound transactions. The attacker allegedly siphoned off an estimated 36.75 BTC worth around $3 million and approximately $7 million in assets between Ethereum, BNB Chain and Base.
Despite the massive scale of the exploit, the protocol has stressed that most of these assets were owned by the protocol and not user deposits. This difference is important because it suggests liquidity providers and traders may have been protected from loss of capital.
Important Announcement
Trading on THORChain is currently halted after a vault was compromised. Initial indications are user funds are safe and only protocol owned funds are affected.
The network automatically detected abnormal behavior and halted signing activity, which alerted…
— THORChain (@THORChain) May 15, 2026
Automatic Safety Systems Minimize Impact
One prominent feature of the incident was real-time response from the network. The current integrated security mechanisms in THORChain spotted deficiencies and stopped signing, ceasing more unauthorized transactions from getting broadcasted. The automated intervention activated the alert across all markets, leading to an immediate halt of trading. The protocol was able to contain the damage and prevent further exploitation by stopping the process quickly.
Their defensive measures highlight the importance of decentralized security design. THORChain’s system does not rely primarily on manual reactions but instead it autonomously detects and responds to threats, which was also key in this case.In addition to the trading freeze, churn activity, the standard process for rotating node operators and reallocating responsibilities, was paused in an effort by developers to maintain system stability while investigating the source of the breach.
Node Operator at Risk of Slashing and Security Audit
The exploit also had an economic impact on node operators associated with the exploited vault. The arrangement means nodes are required to bond the RUNE tokens as collateral under THORChain’s security model, losing more or all of their staked funds if an unauthorized transaction occurs.
As a result, the bonded RUNE of nodes linked to the compromised vault was cut, demonstrating that the protocol is keen on holding its participants accountable and ensuring their risks are shared by all. This method of slashing is carried out in order to allow for security best practices and avoid negligence.
In the wake of the event, THORChain has urged all node operators to conduct urgent reviews of their infrastructure, from host environments and key management processes, to broader operational security protocols.
Operators linked to the affected vault were specifically requested by the team to give Bifrost logs. These logs should be useful in identifying the attack vector and informing remedial measures to prevent reinfection.
The importance of transparency and cooperation is in line with the decentralized nature of the network, which approaches security as a group responsibility.
Network Stability Takes Precedence, Ongoing Investigation
Investigation is still ongoing to ascertain the root cause of the exploit. The developers and contributors are still investigating the breach, with more updates coming as the details unfold. At the same time, a few of the network functions were suspended for some while. The onboarding of additional chains has been called off and processes related to churn are still on hold to ensure system integrity.
Despite such interruptions, THORChain has sought to assure users that key functionalities will go back online when the safety of the chain is guaranteed. The focus is on addressing all the vulnerabilities before normal operation resumes. In particular, early evaluations reveal that although the hack influenced protocol-level components targeted by numerous individual user swaps remain safe.
Wider Implications for Cross-Chain Security in DeFi
This THORChain exploit is an extreme example of the hurdles faced by cross-chain DeFi systems. Although interoperability can unlock significant value, it also creates complex security challenges.
With growing activity across many blockchains, the need for better security architecture becomes apparent. Collectively, automated detection tools, economic deterrents and coordinated incident response frameworks comprise the foundational components needed to create resilient ecosystems.
The next few weeks will be crucial for THORChain. With successful resolution of the breach and bolstering protocol safeguards thereafter, confidence could be restored. On the other hand, if you do not patch underlying vulnerabilities, all concerns surrounding cross-chain liquidity networks will linger.
With the investigation underway, eyes will be firmly fixed on what happens next, and not just for answers only the crash can provide, but also so lessons might be learned which may influence the future of decentralized financial infrastructure.
Disclosure: This is not trading or investment advice. Always do your research before buying any cryptocurrency or investing in any services.
Follow us on Twitter @nulltxnews to stay updated with the latest Crypto, NFT, AI, Cybersecurity, Distributed Computing, and Metaverse news!